How to Check for Malware on Mac
As it's important to check for malware on Mac regularly, we'll explain to you how to do it effectively.
Explore tips and tricks to keep your Mac protected from major digital threats.
As it's important to check for malware on Mac regularly, we'll explain to you how to do it effectively.
We’ll explore some of the most practical Mac malware detection and removal measures you can take.
We’ll look at how to tell if you’re carrying a Trojan, how to get rid of it, and how to prevent future infections.
We’ll show you how to remove this annoying and unwelcome guest from your machine.
We'll get you acquainted with the best ways you can try to remove Bing from Safari, Google Chrome, and Mozilla Firefox—read on to know more about what the Bing redirect virus means.
If your device is already infected, however, don’t panic—We’ll help you fix the problem with several malware Safari removal tips.
Download MacKeeper when you're back at your Mac
or
Please enter your email so we can send you a download link
Check your email on your Mac
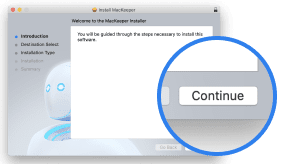
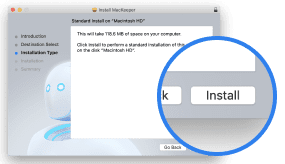
Install MacKeeper on your Mac computer to rediscover its true power.
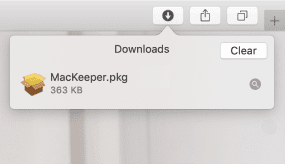
Run Application
Click Continue
Click Install
Your macOS version is lower than OS 10.11. We’d like to offer you MacKeeper 4 to solve the cleaning, privacy, and security issues of your macOS.